par Loïc Mercier Des Rochettes | Juin 5, 2025 | Communauté, Gestion des Identités, SSO
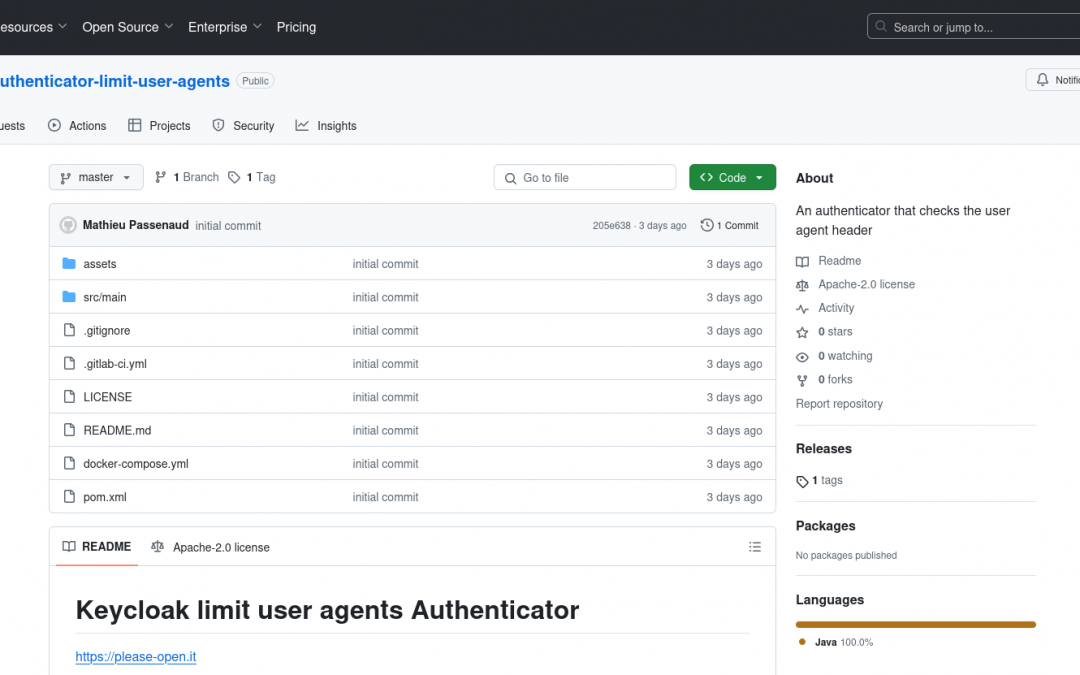
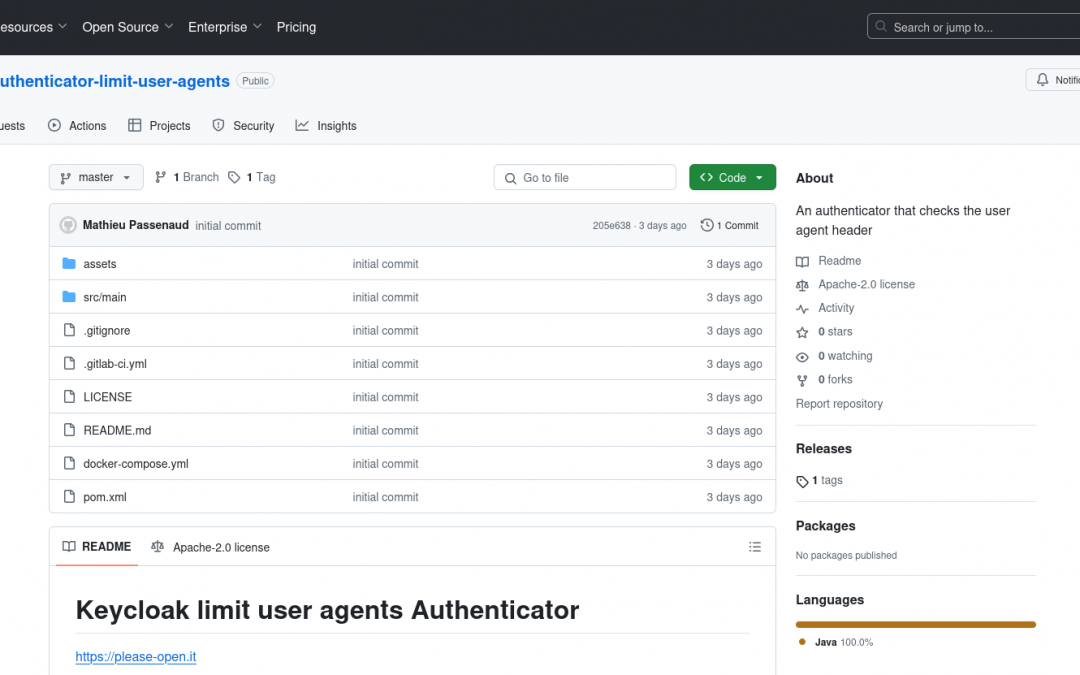
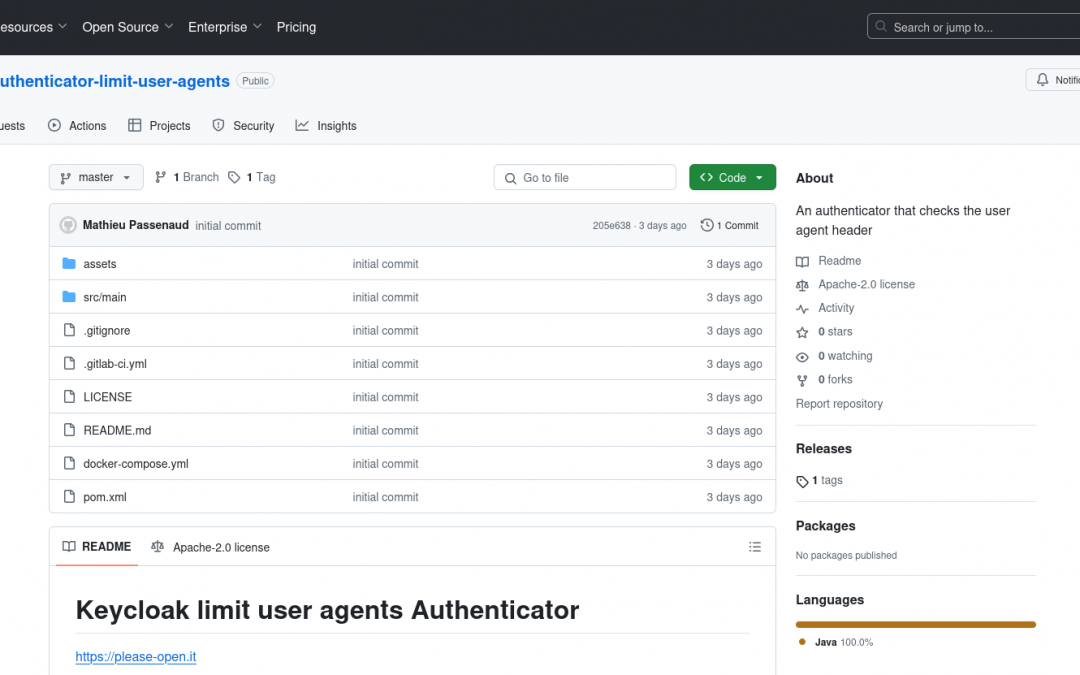
Keycloak User Agent Filter Authenticator: our main partner, Please Open It, created an authenticator that filters the user-agent header for Keycloak to exclude embedded webviews, ensuring compliance with specification requirements. The component reduces the attack...
par Loïc Mercier Des Rochettes | Oct 3, 2024 | Communauté, Gestion des Identités, LDAP, Open Source, SSO
Get rid of your old Active directory/LDAP with keycloak and a small piece of custom software : just a POC for a LDAP bind proxy to log to KeyCloak with LDAP. TL;DR How to spawn a simple bind LDAP proxy for keycloak OIDC password grant in a nutshell. Disclaimer and...
par Mathieu PASSENAUD | Août 21, 2024 | Communauté, Open Source, SSO
This article will share how to enrich native metrics in Keycloak with Micrometer and add yours. Special thanks Thanks to all contributors who built one of the most use Keycloak plugin : https://github.com/aerogear/keycloak-metrics-spi TL/DR We developed a new metrics...
par Mathieu PASSENAUD | Déc 1, 2023 | Communauté, Gestion des Identités, Sécurité, SSO
This article to share how we use Keycloak OIDC authentication with N8N workflow used internally. Please Open It has its own instance of n8n for internal automations : billing, emails etc… Connecting applications to each other is simpler, especially on data management...
par Mathieu PASSENAUD | Nov 13, 2023 | Communauté, Gestion des Identités, Sécurité, SSO
After many years in consulting, how we build our own authorizations platform using KeyCloak. Authn VS Authz First of all, we have to define with a high precision where the authentication stops and where authorization starts. Sometimes you can see posts about : ABAC :...
par Mathieu PASSENAUD | Oct 10, 2023 | Communauté, Gestion des Identités, Sécurité
As is, Keycloak has a default configuration which can introduce security flaws despite your manual testing, that why our partner Please Open It developed this Keycloak Config Checker to help you enforce your security practices. Default configurations As is, Keycloak...