ReCyF / NIS2: IAM at the heart of cyber compliance : The ReCyF (French Cybersecurity Framework), published by ANSSI in March 2026, is the operational reference document for anticipating the French transposition of NIS2. Among its 20 security objectives, Objective 10 — Identity and Access Management (IAM) — is a central pillar, required of both Important Entities (IE) and Essential Entities (EE). This article breaks down these requirements and explains how a sovereign IAM solution like Keycloak addresses them.
1. Context: NIS2 and the ReCyF framework in France
The European NIS2 directive should have been transposed into French law by 17 October 2024. In practice, transposition has been significantly delayed — a bill is still awaiting consideration in the French National Assembly, and the effective entry into force of obligations is now expected for late 2026 / early 2027.
In response to this delay, ANSSI published ReCyF v2.5 on 17 March 2026 at the Campus Cyber — a structuring working document that enables organizations to act proactively. ReCyF defines 20 security objectives organized around 4 pillars:
- Security governance
- Information systems protection
- Detection and resilience
- Enhanced requirements for Essential Entities (EE)
The framework is aligned with ISO 27001 and distinguishes two levels of requirement: Important Entities (IE) and Essential Entities (EE), the latter being subject to additional obligations.
| Key Timeline 17 Oct. 2024: European NIS2 deadline (missed by France) 17 Mar. 2026: ReCyF v2.5 published by ANSSI July 2026: probable French transposition Late 2026 / early 2027: IE/EE obligations enter into force |
Sources :
https://digital-strategy.ec.europa.eu/en/policies/nis2-directive
2. Objective 10: Identity and Access Management
ReCyF Security Objective 10 requires covered entities to implement two major functional blocks:
- Identification and authentication mechanisms for users and automated processes
- Access rights management processes: attribution based on operational need, revocation upon role change, and regular review
2.1 Identification
ReCyF requires each user and automated process to have an individual account. Shared accounts are only tolerated when technically justified and must be accompanied by compensatory traceability measures. Obsolete accounts must be deactivated within the timeframes defined by internal policy (the framework cites 7 days as an example), and an annual account review is mandatory.
2.2 Authentication
All access must be protected by an authentication mechanism involving at least one secret element. Authentication factors must comply with ANSSI recommendations on complexity. Default secret elements must be changed before any resource is put into service, and shared account credentials must be renewed whenever a user leaves the group.
For Essential Entities only, traceability of access is required when the secret element cannot be changed for technical reasons.
2.3 Access Rights
The principle of least privilege is central to Objective 10: rights are granted only to authenticated users, and only for the resources necessary for their specific missions. An annual review of access rights is mandatory to verify compliance and correct anomalies.
| Summary Table — IAM Requirements — ReCyF v2.5 Objective 10 |
| Reference | Requirement | IE | EE |
| 10.A.1 | Individual accounts for each user and automated process | ✓ | ✓ |
| 10.A.2 | Account used exclusively by its assigned holder | ✓ | ✓ |
| 10.A.3 | Compensatory measures for shared accounts (traceability) | ✓ | ✓ |
| 10.A.5 | Deactivation of obsolete accounts within defined timeframes | ✓ | ✓ |
| 10.A.6 | Account review at least once per year | ✓ | ✓ |
| 10.B.1 | Authentication with at least one secret element | ✓ | ✓ |
| 10.B.2 | Change default secrets before putting resources into service | ✓ | ✓ |
| 10.B.5 | Compliance with ANSSI recommendations on authentication factors | ✓ | ✓ |
| 10.B.7 | Access traceability if secret is fixed (technical exception) | – | ✓ |
| 10.C.1 | Rights granted only to authenticated users | ✓ | ✓ |
| 10.C.2-3 | Least privilege principle (operational need basis) | ✓ | ✓ |
| 10.C.4 | Annual review of access rights | ✓ | ✓ |
IE: Important Entity — EE: Essential Entity — ✓: required — –: not applicable
3. Why sovereign IAM is the structural answer
3.1 The dual regulatory challenge
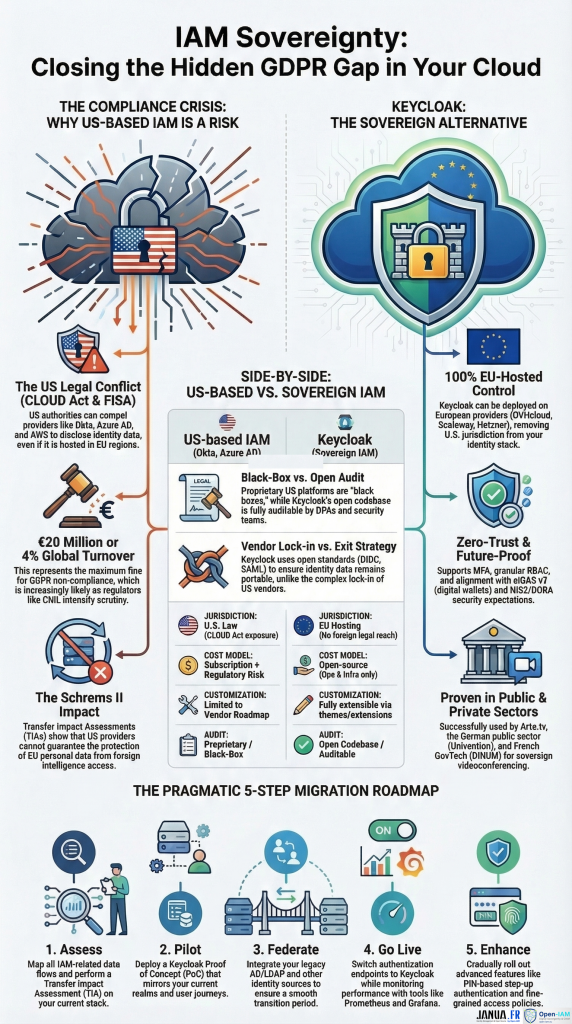
Organizations covered by NIS2/ReCyF face a dual challenge: meeting the technical requirements of Objective 10, while ensuring the legal sovereignty of their IAM infrastructure. The dominant American solutions — Okta, Microsoft Entra ID (formerly Azure AD), AWS Cognito — are subject to the CLOUD Act (2018) and FISA, which authorize US authorities to demand access to data even when hosted in Europe. This creates a structural conflict with the GDPR (Schrems II ruling) that Transfer Impact Assessments (TIAs) often cannot resolve.
| Concrete financial risk GDPR sanctions can reach €20M or 4% of global annual turnover. France’s CNIL is already investigating Microsoft 365, including identity federation. |
3.2 Keycloak: the solution that checks every box
Keycloak, open source under the Apache 2.0 license, addresses each requirement of Objective 10 while guaranteeing full legal sovereignty:
- Individual accounts and fine-grained rights management: native realm, role, group, and access policy management
- Strong authentication: MFA, TOTP, WebAuthn/FIDO2, step-up authentication for sensitive operations
- Standardized protocols: OAuth2, OpenID Connect, SAML 2.0 — zero vendor lock-in
- Traceability and audit: comprehensive audit logs, open source code auditable by your security teams
- Account review automation: API and admin console enabling automated periodic access reviews
- Sovereign hosting: deployable on OVHcloud, Scaleway, Hetzner, or as PaaS on Clever Cloud
Organizations like Arte.tv (France/Germany) have already migrated to Keycloak hosted on European infrastructure, moving away from American providers to ensure compliance. The French public sector (DINUM) and the German public sector also use Keycloak in sensitive environments.
4. Practical roadmap for IE and EE organizations
To anticipate compliance before obligations enter into force (late 2026 / early 2027), the following steps are recommended:
| 1 · Assess | Map existing IAM flows. Conduct a TIA on the current stack to identify CLOUD Act / Schrems II risks. |
| 2 · PoC | Deploy a Keycloak Proof of Concept mirroring your existing realms and clients. Validate compatibility with your applications. |
| 3 · Federate | Maintain a bridge to the legacy directory (AD/LDAP) during the transition phase (progressive cutover). |
| 4 · Go Live | Redirect authentication endpoints. Set up monitoring (Prometheus/Grafana). Enable audit logs. |
| 5 · Improve | Strengthen: step-up PIN, FIDO2 authentication, eIDAS v2 integration. Automate annual access reviews via the Keycloak API. |
5. Conclusion
ReCyF Objective 10 is not an additional constraint — it is the formalization of a good security practice that every serious organization should already be applying. Rigorous management of identities, authentication, and access rights is the foundation of any effective cyber defense posture.
The question is not whether your organization must comply, but how to do so without creating new legal dependencies that carry their own risks. Keycloak, deployed on sovereign European infrastructure, offers the most complete and durable answer: technical compliance, data control, and architectural freedom.
Act now
French transposition is expected in July 2026. Don’t wait for obligations to enter into force before auditing your IAM. Contact Open-IAM / Janua.fr for a no-commitment compliance diagnostic.
- IAM & Regulatory Compliance - 2 avril 2026
- IAM: The Hidden GDPR Vulnerability in Your Cloud Stack - 19 mars 2026
- New Keycloak online training - 19 janvier 2022