IAM: the hidden GDPR vulnerability in your cloud stack — And how Keycloak fixes it
Continuing the Sovereignty Journey….
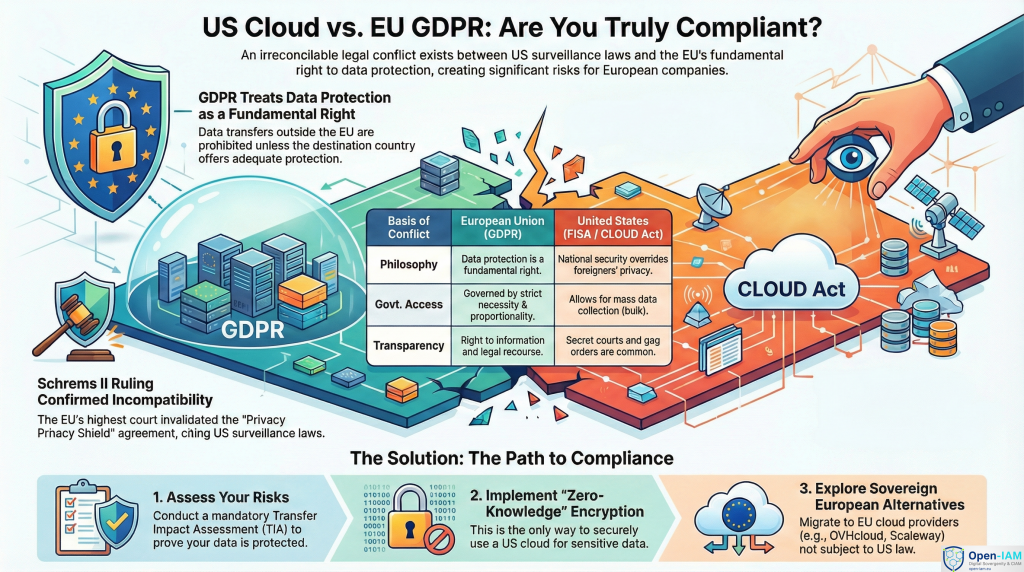
In a previous article, Digital Sovereignty: Why Your European Business Probably Breaks GDPR Law, the focus was on how U.S. cloud hyperscalers such as Microsoft 365, AWS, and Google Cloud expose European organisations to significant regulatory risk through conflicts between the CLOUD Act, FISA, and the GDPR. One area, however, requires particular attention: Identity and Access Management (IAM), which is not just another technical layer but the entry point to all sensitive data — and therefore a central battleground for digital sovereignty.
Why IAM Undermines Sovereignty
An IAM platform stores and manages the most critical elements of your security posture: user identities, credentials, access tokens, logs, and session data — all of which qualify as personal data under the GDPR. Yet most European organisations still depend on U.S.-controlled IAM services, including: Okta/Auth0 and Ping Identity, which fall directly under the CLOUD Act; Microsoft Azure AD/Entra ID, which remains under U.S. jurisdiction even when hosted in EU regions; and AWS IAM/Cognito, where U.S. authorities can compel disclosure of identity data.
The Schrems II ruling did not spare IAM services: Transfer Impact Assessments (TIAs) consistently show that these providers cannot guarantee that U.S. authorities will not access EU personal data. A single data access request or security incident can expose millions of identities and lead to fines of up to €20 million or 4% of global annual turnover, while regulators such as France’s CNIL have already intensified scrutiny on Microsoft 365 and its identity federation mechanisms.
On top of this legal risk, vendor lock-in makes IAM migration complex and costly, which in practice delays any move towards a more sovereign architecture.
Keycloak as a Sovereign Alternative
Keycloak has emerged as a strategic open-source IAM solution at the heart of Europe’s digital sovereignty initiatives. Backed by Red Hat and governed by an open community under the Apache 2.0 licence, Keycloak can be deployed entirely on EU infrastructure providers such as OVHcloud, Scaleway or Hetzner, removing U.S. jurisdiction from the equation.
Capabilities that Support GDPR Compliance
- Comprehensive standards support: OAuth2, OpenID Connect, SAML 2.0 and LDAP for broad interoperability without proprietary lock-in.
- Zero-trust ready: Multi-factor authentication, step-up authentication, granular RBAC, client policies and detailed auditing aligned with NIS2 and DORA expectations.
- Full control over EU data: Self-hosted deployments ensure no identity data leaves your perimeter, with encryption in transit and at rest and integration with sovereign databases such as PostgreSQL on EU infrastructure.
- eIDAS v2 alignment: Support for digital wallets and verifiable credentials, making Keycloak a future-proof building block for the European Digital Identity framework.
Keycloak is proven in environments ranging from SMEs to very large-scale deployments, with clustering options enabling high availability and resilience.
Examples of Sovereign Deployments
- Arte.tv (France/Germany): Migration to a Keycloak-based architecture on Scaleway, in particular to meet public-sector compliance requirements and reduce exposure to U.S. cloud providers.
- German public sector: Integration of Keycloak within Univention Corporate Server (UCS) to deliver SSO in sensitive environments.
- French GovTech initiatives: Use of Keycloak in DINUM projects such as the Visio sovereign videoconferencing platform.
Janua’s partner please-open.it operates a Keycloak-as-a-Service model for enterprises, demonstrating that large-scale migrations can be delivered in a matter of months.
Keycloak Compared to Proprietary IAM Platforms
| Aspect | U.S.-based IAM (Okta, Azure AD, etc.) | Keycloak (Sovereign IAM) | |
| Jurisdiction | U.S. law, including CLOUD Act exposure | EU hosting with no foreign legal reach | |
| Cost model | Recurring subscription plus regulatory risk | Open-source; infrastructure and operations only | |
| Customisation | Constrained by vendor roadmap | Fully extensible via themes and extensions | |
| Exit strategy | Complex migrations and strong lock-in | Open standards and portable identity data | |
| Audit and oversight | Black-box architecture | Open codebase, auditable by CNIL/DPAs | |
A Pragmatic Migration Roadmap
- Assess: Map IAM-related data flows and perform a TIA on the existing stack.
- Pilot: Deploy a Keycloak proof of concept mirroring current realms, clients and main user journeys.
- Federate: Integrate legacy AD/LDAP and other sources of identity during the transition period.
- Go live: Switch authentication endpoints to Keycloak and monitor performance and security with tools such as Prometheus and Grafana.
- Enhance: Gradually add advanced features such as PIN-based step-up authentication and fine-grained policies.
Janua.FR/Open-IAM supports organisations throughout this journey, with a focus on minimising operational disruption while restoring control over identity data.
From Optional Choice to Strategic Imperative
IAM sovereignty has become a strategic necessity rather than a purely technical option. With ongoing regulatory investigations and the prospect of future rulings comparable to Schrems III, continued reliance on U.S.-controlled IAM solutions represents a structural compliance and business risk, whereas Keycloak offers a credible path to regain control, strengthen compliance, and optimise costs.
Ready to assess your IAM posture? Janua.FR/Open-IAM can provide a tailored sovereignty review of your current environment.
Disclaimer: This document is provided for informational purposes only and does not constitute legal advice; organisations should consult qualified legal counsel for guidance specific to their jurisdiction and use cases.
- IAM: The Hidden GDPR Vulnerability in Your Cloud Stack - 19 mars 2026
- New Keycloak online training - 19 janvier 2022
- Sizing Keycloak or Redhat SSO projects - 8 juin 2021