In this article, we will try to synthesize about Multi Factor Authentication with Keycloak and RedHat SSO.
Presentation
MFA stands For multi-factor authentication. Usual authentication with username/password is one of the weakest authentication scheme possible, which presents a security vulnerability. Therefore adding another factor such as OTP or biometrics enforce authentication security hardening.
Keycloak OTP MFA versus SMS-OTP
Keycloak provides out of the box OTP MFA which can be easily rolled out.
Keycloak OTP MFA is relying on a challenge code which can be delivered by google authenticator or Free OTP.
Keycloak it is based on TOTP (time based OTP). Whereas it is very easy to forge identity with SMS-OTP (recovering SMS challenge code with a SMS spyertracker), this is totally impossible with Keycloak OTP as the challenge code is never send out externally.
Compared to system using SMS-OTP, Keycloak OTP MFA is very secure.
LOA concepts and MFA usage
LOA stands for level of authentication
In an ideal world, customer would need to have the following within a realm:
- (1) Some client applications using simple authentication (username/password)
(low authentication level privilege) - (2) Some client applications able to perform mfa (Username/password+ otp or other authenticator)
(high authentication level privilege) - (3) possibility to navigate between the different applications of the realm using the SSO token
In term of requirements, it would mean that:
- It should be possible to configure the client authentication flow on a per application basis
- (2) In order to be able to navigate between the different clients using the SSO token (3), it is also necessary to use a LOA (level of authentication)
- For example a user which is authenticated using a low level authentication application privilege will require an elevation of privilege to be able to authenticate against application using mfa
- This elevation of privilege entails filling up OTP challenge information.
Keycloak/RH-SSO Authentication flow and MFA
In previous section has been presented the high level concepts of LOA and MFA, thow o be able to authenticate at different level for client application within a realm and also to navigate between application using stepping-up and loa mechanisms.
Now let’s see what is available with keycloak/Redhat SSO
RH-SSO 7.2/ (Keycloak 3.4.3)
- OTP provided out of the box
- possibility to create new authenticator for the authentication flow using keycloak spi
- authentication on a per realm basis
As a consequence, it means that if customer needs applications with different authentication scheme such simple as simple authentication and mfa, this will have entail the creation of different realms
Keycloak 4.6 (Latest)
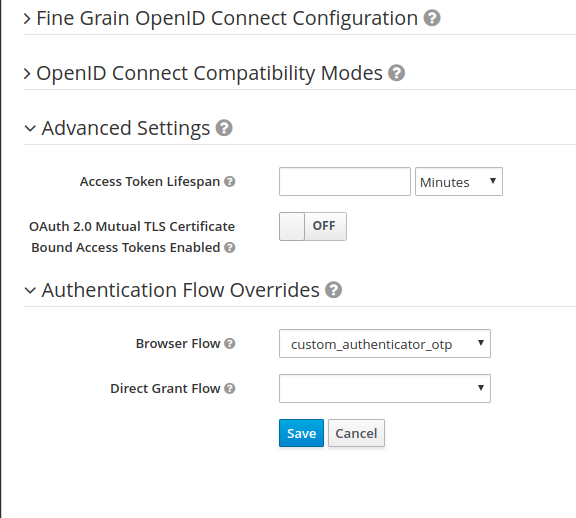
Keycloak 4.6 provides what is available within keycloak 3.43 with some additional tweaks which can be found on a client page such as authentication flow overrides.
This feature does not expose the notion of LOA (level of authentication), and does not seem to be very documented in keycloak document documentation.
Upcoming release 5.X – Jira tickets
Many JIRA tickets have been been created for the requirements mentioned in this chapter (realm authentication level, LOA, stepping up) and marked for keycloak 5.X
It means that Redhat is considering those points as very important, and should be available in an upcoming major keycloak release.
- https://issues.jboss.org/browse/KEYCLOAK-847 Step up authentication
- https://issues.jboss.org/browse/KEYCLOAK-3314 acr/amr support
- KEYCLOAK-4182 Improve support for two factor authentication
https://issues.jboss.org/browse/KEYCLOAK-4182?_sscc=t - KEYCLOAK-6769 Multi-factor authentication and its corresponding « acr » value in ID Token
- https://lists.jboss.org/pipermail/keycloak-dev/2017-August/009821.html
- [keycloak-user] adding realm level configuration parameter https://lists.jboss.org/pipermail/keycloak-user/2018-January/012843.html
- Step-up Authentication for Keycloak https://lists.jboss.org/pipermail/keycloak-dev/2017-April/009246.html
- Step-up Authentication for Keycloak https://lists.jboss.org/pipermail/keycloak-dev/2017-April/009245.html
- [keycloak-user] Authentication level realm
- https://lists.jboss.org/pipermail/keycloak-user/2016-September/007504.html
Keycloak/RH-SSO MFA synthesis
Keycloak provides out of the box a very good MFA solution OTP based.
- It is very easy to put in place
- It is very reliable as implemented using TOTP/HMAC technology
- It is possible to write/customize its own authenticator using Keycloak SPI
- Current RH-SSO//keycloak does not provide LOA or stepping to allow to have application using different authentication level within a single realm, but many tickets have been craeted upon this topic on keycloak release 5.X, which makes keycloak very promising
As a whole, keycloak all the current available MFA feature and upcoming features make keycloak a very attractive and appealing product to perform authentication out of the of the box.
- New Keycloak online training - 19 janvier 2022
- Sizing Keycloak or Redhat SSO projects - 8 juin 2021
- Keycloak.X Distribution - 28 janvier 2021